✨ Learning points
This application presents a unique opportunity to learn about mobile device security and privacy. It serves as a practical example of how seemingly passive devices can be monitored and how user data, even the act of unauthorized access, can be logged. Teaching elements center around understanding digital footprints, user consent, and the implications of granting permissions to apps.
Permission Awareness
The app highlights the importance of understanding app permissions. Discussing this can be an engaging teaching moment about digital literacy and responsible app usage. Consider exploring the Android permission model in detail.
💡 Innovation guidance
The core innovation lies in its proactive approach to security. Instead of simply reacting to breaches, it aims to deter unauthorized access. This concept can inspire discussions on preventative security measures in other contexts. Innovation lessons involve thinking outside the box and anticipating potential threats before they materialize.
- Thinking Preventatively: How can we design systems that anticipate and prevent security breaches?
- User-Centric Security: How can security measures be implemented without compromising user experience?
🔎 Discovery paths
Using this application opens discovery paths into ethical hacking and penetration testing (within legal and ethical boundaries). Students can explore how similar techniques are used to identify vulnerabilities in larger systems. Discovery methods include reverse engineering, code analysis, and threat modeling.
Ethical hacking involves using hacking techniques to identify and fix vulnerabilities in a system, with the permission of the system owner.
🌱 Growth moments
Implementing similar security features requires a solid understanding of mobile operating systems and programming languages. Growth strategies involve learning about API usage, background processing, and data storage methods. These moments can encourage students to pursue further studies in computer science and cybersecurity.
- Mastering Android SDK.
- Learning about background services.
- Implementing secure data storage.
🚀 Breakthrough insights
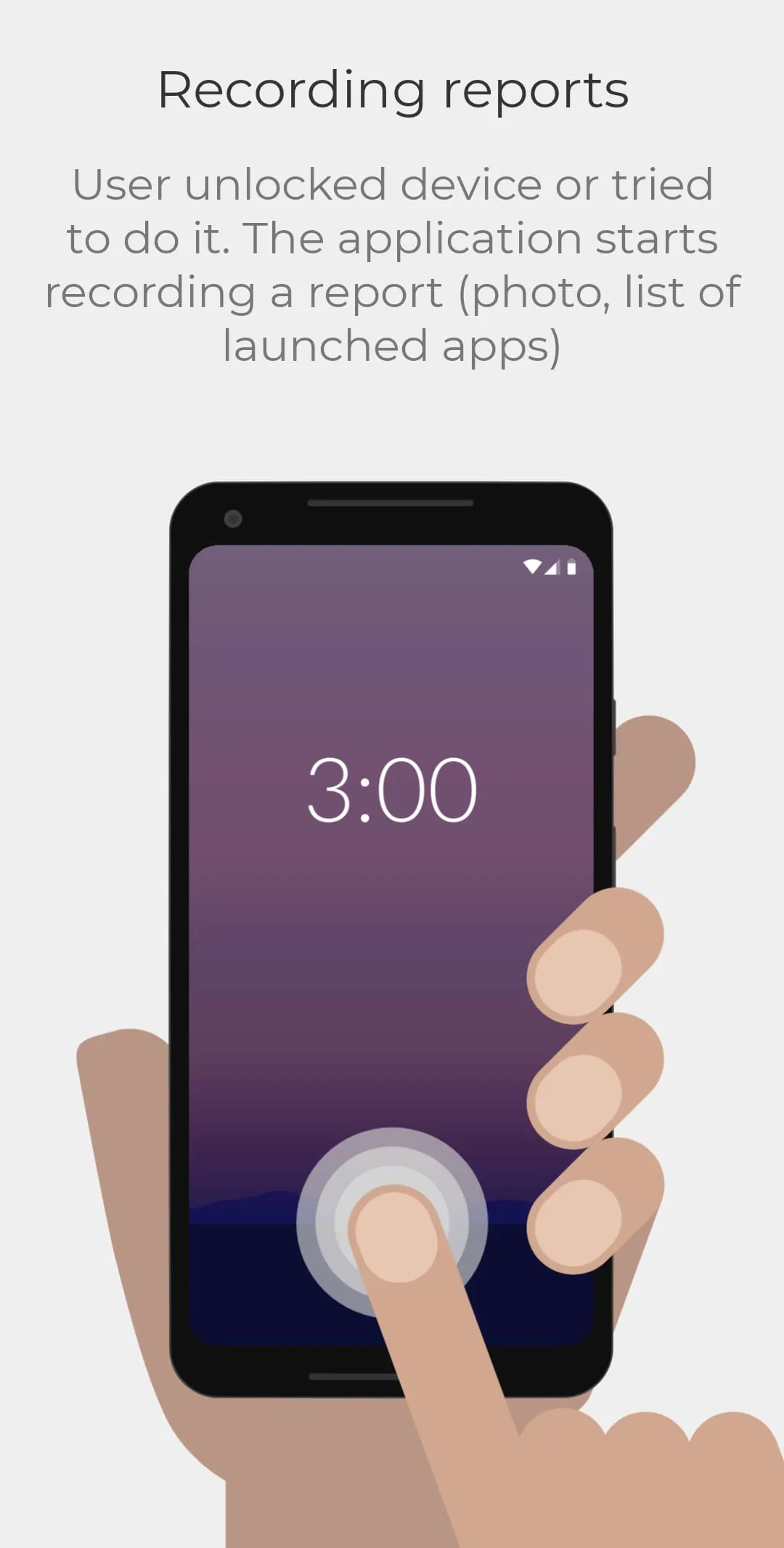
The application's ability to detect unauthorized access relies on system-level monitoring and event logging. This breakthrough insight can lead to understanding how operating systems manage security events and how these events can be leveraged for security purposes. Breakthrough steps involve exploring operating system internals and security frameworks.
- Proactive security measure
- Simple and easy to use
- Raises awareness about device security
- Potential privacy concerns
- Battery consumption
- Limited functionality in free version
Overall learning value
The application offers significant learning value by demonstrating practical security concepts and inspiring further exploration into mobile security and cybersecurity. It's a valuable tool for teaching digital literacy and responsible technology use.